My Approach
This project is built to simplify cybersecurity for SMEs by translating complex risks into clear, human-focused strategies. Rooted in behavioural insight and storytelling, my approach focuses on identifying gaps, visualising threats, and equipping businesses with scalable protection—from risk registers to incident response.
Vision and Innovation
My vision is to reimagine how cybersecurity consulting is delivered: not just as a technical checklist, but as a strategic, human-first experience. I bring together security frameworks, creative communication, and research-backed insights to help clients understand their exposure and make smart decisions that protect their operations and reputation.
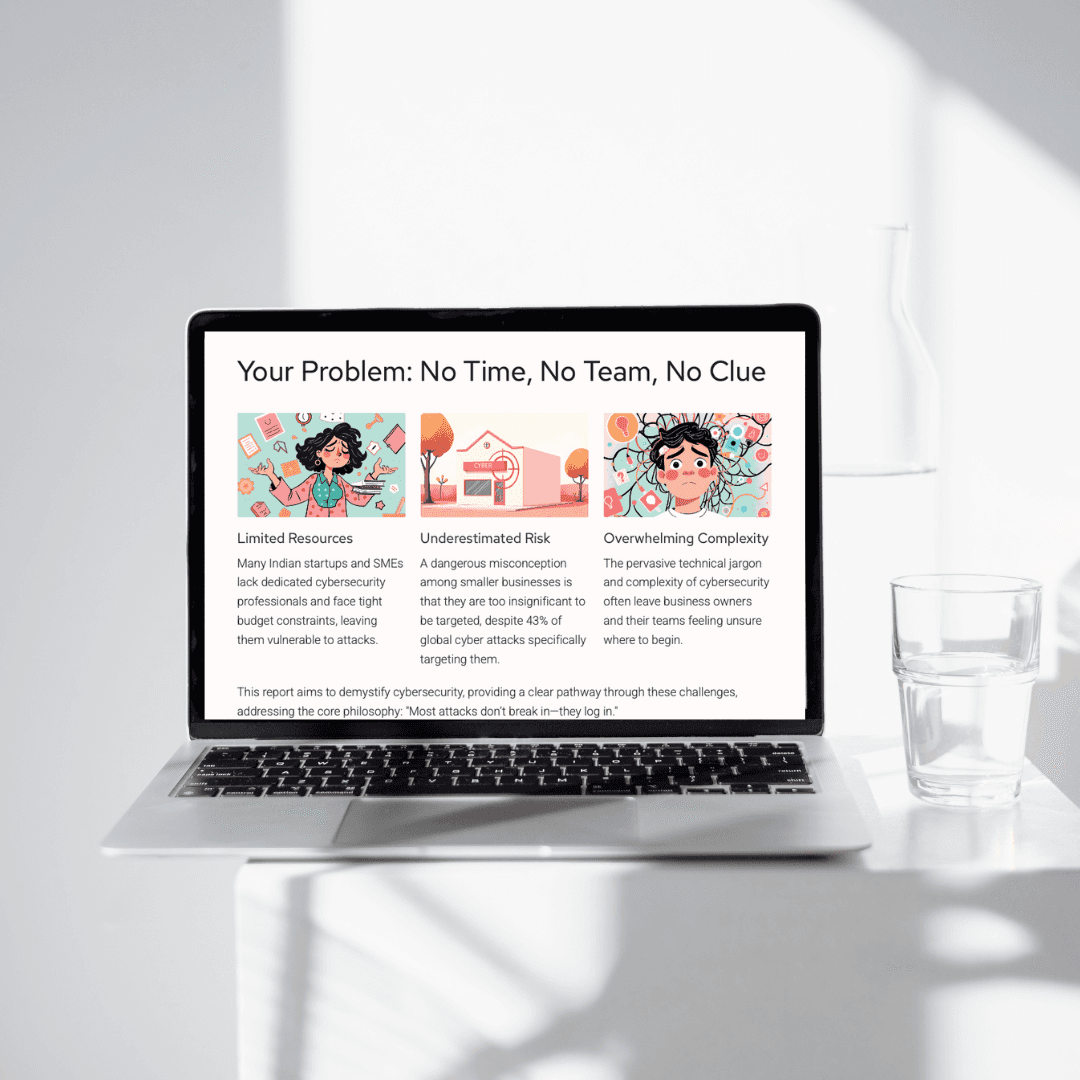
Identifying Unique Challenges
SMEs often struggle with the invisible nature of cyber threats. Unlike visible physical damage, breaches can quietly unfold over time. I address this by uncovering overlooked assets, assessing psychological vulnerabilities (like social engineering), and mapping threat surfaces with clarity and empathy.
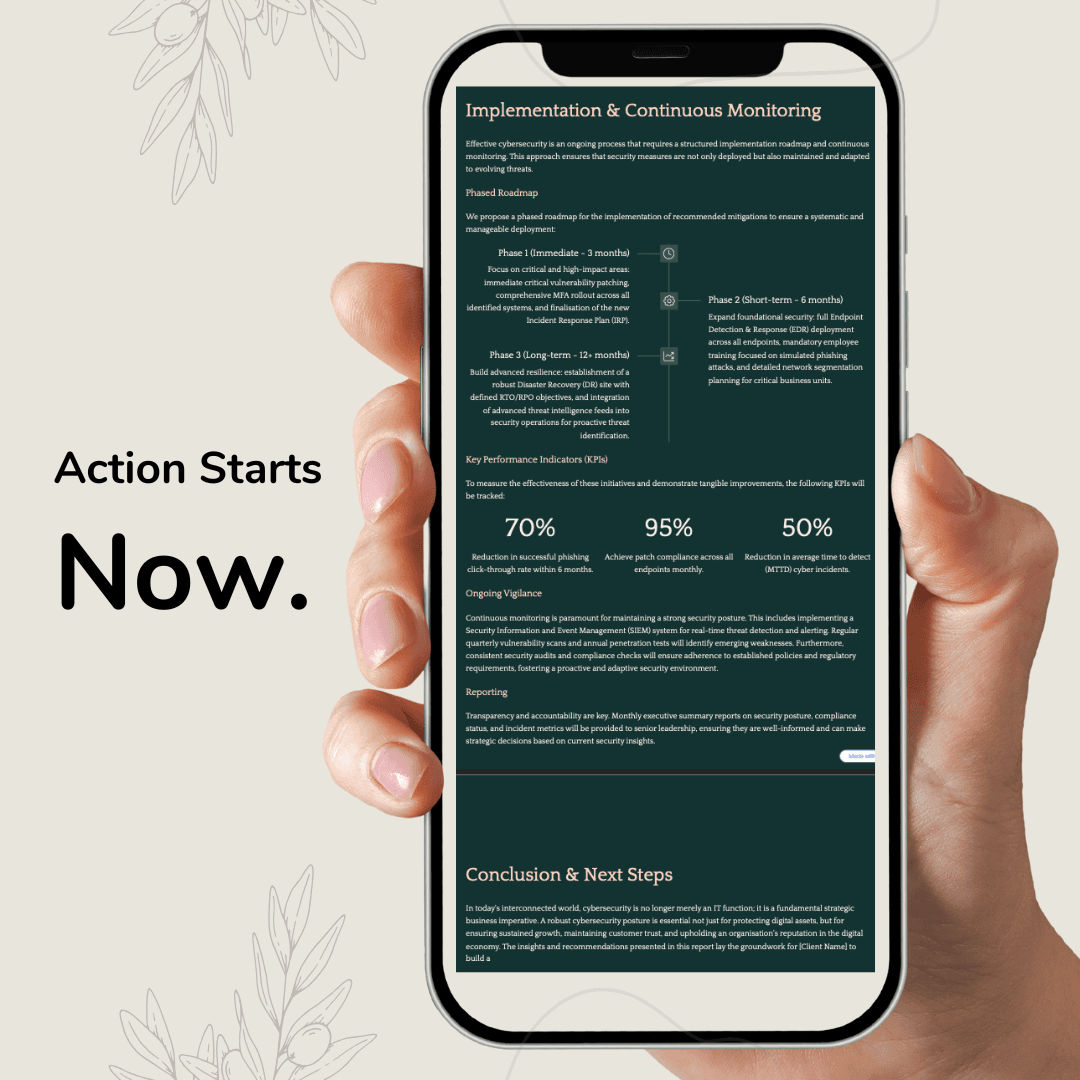
Resolving Complex Problems
By merging cybersecurity expertise with business storytelling, I help organisations build comprehensive risk reports. These include asset inventories, threat maps, risk registers, mitigation matrices, and implementation roadmaps. Each solution is designed to be low-friction, high-impact, and actionable within real-world resource limits.
User-Centric Design
Every output—from risk reports to dashboards—is designed for usability. I prioritise clarity over jargon, provide visual frameworks like risk matrices, and make cybersecurity feel accessible rather than overwhelming. Whether it’s a workshop or a digital handover, my content is built to engage and empower.
Meeting User Needs
Today’s SMEs don’t just want a firewall—they want clarity, resilience, and peace of mind. I meet that need with structured documentation, easy-to-digest visuals, and step-by-step mitigation plans. Everything is backed by compliance standards, but delivered in plain English.
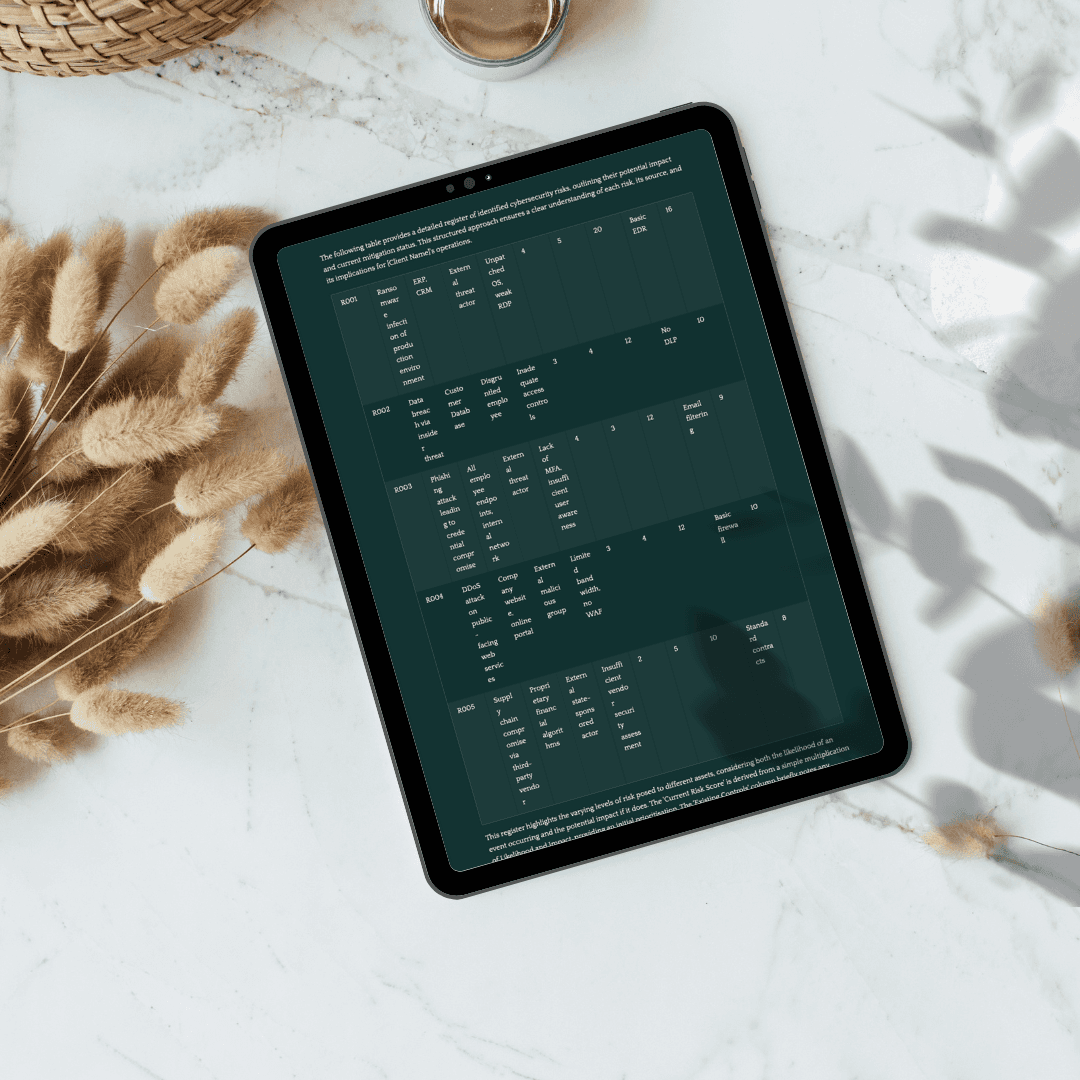
Detailed Deliverables
Introductory Risk Report: High-level threat awareness
Risk Identification & Register: Assets, vulnerabilities, threat mapping
Risk Matrix & Analysis: Visual severity grid + insights
Mitigation Plan: Preventive, detective, corrective controls
Implementation Timeline: Simple rollout with performance KPIs
Incident Response Plan: SME-ready action guide
Review Framework: Ongoing evaluation strategy
Accessibility and Reporting
My work is built for SMEs—clean, visual, readable, and easy to implement. Reports are formatted for web or print, with summary dashboards and detailed breakdowns. You don’t need a security background to use them—you just need a willingness to protect what matters.
Conclusion
Cybersecurity isn’t just a technical need—it’s a trust-building tool. I offer a consulting experience designed to demystify cyber risk, humanise defence, and make security a strategic advantage. Through every project, my goal is to help businesses build confidence, resilience, and readiness in a connected world.