100+ Happy Clients



100+ Happy Clients
Hi, I'm Muhammad!
Hi, I'm Muhammad!
Cybersecurity Consultant
HTML5/CSS3 Mastery
Product Design
Branding
Collaborative Team Player
Cybersecurity Consultant
HTML5/CSS3 Mastery
Product Design
Branding
Collaborative Team Player



























About Me
Greetings! I’m a Cybersecurity Risk Management student at the University of Galway who loves breaking down complex topics through storytelling. I’ve spoken at events for over 3,500 students and led winning hackathon and case competition teams. I believe good communication makes security stronger.
Greetings! I’m a Cybersecurity Risk Management student at the University of Galway who loves breaking down complex topics through storytelling. I’ve spoken at events for over 3,500 students and led winning hackathon and case competition teams. I believe good communication makes security stronger.
Greetings! I’m a Cybersecurity Risk Management student at the University of Galway who loves breaking down complex topics through storytelling. I’ve spoken at events for over 3,500 students and led winning hackathon and case competition teams. I believe good communication makes security stronger.
I’ve volunteered 500+ hours across 15+ university societies. Whether I’m supporting environmental causes, building cultural communities, or helping students feel welcome, I enjoy working with people and creating space for others to grow.
I’ve volunteered 500+ hours across 15+ university societies. Whether I’m supporting environmental causes, building cultural communities, or helping students feel welcome, I enjoy working with people and creating space for others to grow.
I’ve volunteered 500+ hours across 15+ university societies. Whether I’m supporting environmental causes, building cultural communities, or helping students feel welcome, I enjoy working with people and creating space for others to grow.
Before Galway, I ran a PlayStation rental business in India that made €25,000 in revenue. Now, I mix that business mindset with tech skills—from coding apps to building AI solutions. I like solving problems, staying curious, and sharing what I learn.
Before Galway, I ran a PlayStation rental business in India that made €25,000 in revenue. Now, I mix that business mindset with tech skills—from coding apps to building AI solutions. I like solving problems, staying curious, and sharing what I learn.
Before Galway, I ran a PlayStation rental business in India that made €25,000 in revenue. Now, I mix that business mindset with tech skills—from coding apps to building AI solutions. I like solving problems, staying curious, and sharing what I learn.
Kind words from Teams
Testimonials

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”

Joanna Maj
Public Relations Officer, CompSoc
"Working with Muhammad Murtuza during the legal tech hackathon was a great experience—his teamwork and storytelling skills brought our project to life and helped elevate the entire team, ultimately enabling us to win top spots."

Abbi Fritz
Auditor, Enviornment Society
"Muhammad Murtuza Hussain brought clarity and structure to our society’s finances as Treasurer of the Environment Society. He recovered reimbursements, streamlined budgeting, and built trust through clear communication. His dedication and leadership made a lasting impact, and I’m confident he’ll add value to any future team."

Yanan Li
Cybersecurity Graduate
“Working with Muhammad Murtuza on the KA-SAT cybersecurity incident was a deeply insightful experience. His structured approach to risk identification, mitigation planning, and framework application brought clarity and precision to our assessment. From building detailed risk matrices and registers to aligning with industry standards like NIST, his contributions ensured our analysis was both technically sound and strategically actionable. He brings not just expertise, but also a strong sense of ownership and collaboration to every project.”
My Stack


Tableau helps me turn raw data into compelling, interactive visual stories. I use it to create dashboards that reveal trends, monitor KPIs, and support decision-making in security analytics, social media reporting, and business strategy. It’s essential for translating complex data into actionable insights.
Tableu
Tableau helps me turn raw data into compelling, interactive visual stories. I use it to create dashboards that reveal trends, monitor KPIs, and support decision-making in security analytics, social media reporting, and business strategy. It’s essential for translating complex data into actionable insights.
Tableu
Tap to flip
Tableau helps me turn raw data into compelling, interactive visual stories. I use it to create dashboards that reveal trends, monitor KPIs, and support decision-making in security analytics, social media reporting, and business strategy. It’s essential for translating complex data into actionable insights.
Tableu
Tap to flip
ChatGPT is my content generation and assistance tool. I leverage it for content ideas, copywriting, and problem-solving. It provides invaluable insights and suggestions that enhance the quality of my projects.
ChatGPT
ChatGPT is my content generation and assistance tool. I leverage it for content ideas, copywriting, and problem-solving. It provides invaluable insights and suggestions that enhance the quality of my projects.
ChatGPT
Tap to flip
ChatGPT is my content generation and assistance tool. I leverage it for content ideas, copywriting, and problem-solving. It provides invaluable insights and suggestions that enhance the quality of my projects.
ChatGPT
Tap to flip
Notion helps me keep my projects organized. I use it for project management, task tracking, and as a central hub for documentation, ensuring that everything from design notes to project timelines is in one place.
Notion
Notion helps me keep my projects organized. I use it for project management, task tracking, and as a central hub for documentation, ensuring that everything from design notes to project timelines is in one place.
Notion
Tap to flip
Notion helps me keep my projects organized. I use it for project management, task tracking, and as a central hub for documentation, ensuring that everything from design notes to project timelines is in one place.
Notion
Tap to flip
Wireshark is my go-to tool for deep packet inspection and network diagnostics. I use it to analyse traffic in real time, helping identify vulnerabilities, unusual patterns, and potential breaches. It’s essential for transparent network monitoring during audits and investigations.
Wireshark
Wireshark is my go-to tool for deep packet inspection and network diagnostics. I use it to analyse traffic in real time, helping identify vulnerabilities, unusual patterns, and potential breaches. It’s essential for transparent network monitoring during audits and investigations.
Wireshark
Tap to flip
Wireshark is my go-to tool for deep packet inspection and network diagnostics. I use it to analyse traffic in real time, helping identify vulnerabilities, unusual patterns, and potential breaches. It’s essential for transparent network monitoring during audits and investigations.
Wireshark
Tap to flip
Kali Linux serves as my penetration testing environment, packed with powerful tools for ethical hacking. From reconnaissance to exploitation, I use it to simulate attacks and assess system resilience—crucial for identifying weak points before adversaries do.
Kali Linux
Kali Linux serves as my penetration testing environment, packed with powerful tools for ethical hacking. From reconnaissance to exploitation, I use it to simulate attacks and assess system resilience—crucial for identifying weak points before adversaries do.
Kali Linux
Tap to flip
Kali Linux serves as my penetration testing environment, packed with powerful tools for ethical hacking. From reconnaissance to exploitation, I use it to simulate attacks and assess system resilience—crucial for identifying weak points before adversaries do.
Kali Linux
Tap to flip
Burp Suite is my preferred platform for web application testing. I use it to intercept traffic, identify vulnerabilities like XSS or SQL injection, and test authentication mechanisms. It plays a key role in ensuring secure and robust web services.
BurpSuite
Burp Suite is my preferred platform for web application testing. I use it to intercept traffic, identify vulnerabilities like XSS or SQL injection, and test authentication mechanisms. It plays a key role in ensuring secure and robust web services.
BurpSuite
Tap to flip
Burp Suite is my preferred platform for web application testing. I use it to intercept traffic, identify vulnerabilities like XSS or SQL injection, and test authentication mechanisms. It plays a key role in ensuring secure and robust web services.
BurpSuite
Tap to flip
Splunk enables real-time security monitoring through log analysis and event correlation. I use it to investigate incidents, build detection rules, and generate actionable insights—making it central to threat detection and response workflows.
splunk
Splunk enables real-time security monitoring through log analysis and event correlation. I use it to investigate incidents, build detection rules, and generate actionable insights—making it central to threat detection and response workflows.
splunk
Tap to flip
Splunk enables real-time security monitoring through log analysis and event correlation. I use it to investigate incidents, build detection rules, and generate actionable insights—making it central to threat detection and response workflows.
splunk
Tap to flip
Python is my foundational scripting and automation language for cybersecurity workflows. I use it to build scanning scripts, automate assessments, parse logs, and prototype security tools. Its flexibility and massive ecosystem make it indispensable for both red and blue team tasks.
Python
Python is my foundational scripting and automation language for cybersecurity workflows. I use it to build scanning scripts, automate assessments, parse logs, and prototype security tools. Its flexibility and massive ecosystem make it indispensable for both red and blue team tasks.
Python
Tap to flip
Python is my foundational scripting and automation language for cybersecurity workflows. I use it to build scanning scripts, automate assessments, parse logs, and prototype security tools. Its flexibility and massive ecosystem make it indispensable for both red and blue team tasks.
Python
Tap to flip
Zapier is my automation powerhouse for connecting tools and streamlining workflows without writing code. I use it to automate reporting, integrate cybersecurity alerts, and simplify social media content pipelines—saving time while enhancing consistency across platforms.
Zapier
Zapier is my automation powerhouse for connecting tools and streamlining workflows without writing code. I use it to automate reporting, integrate cybersecurity alerts, and simplify social media content pipelines—saving time while enhancing consistency across platforms.
Zapier
Tap to flip
Zapier is my automation powerhouse for connecting tools and streamlining workflows without writing code. I use it to automate reporting, integrate cybersecurity alerts, and simplify social media content pipelines—saving time while enhancing consistency across platforms.
Zapier
Tap to flip
Slack is the cornerstone of my collaborative workflow. It fosters a dynamic environment where teams can seamlessly exchange ideas, share files, and provide real-time feedback.
Slack
Slack is the cornerstone of my collaborative workflow. It fosters a dynamic environment where teams can seamlessly exchange ideas, share files, and provide real-time feedback.
Slack
Tap to flip
Slack is the cornerstone of my collaborative workflow. It fosters a dynamic environment where teams can seamlessly exchange ideas, share files, and provide real-time feedback.
Slack
Tap to flip
Adobe Creative Cloud is my comprehensive toolkit for unleashing creative potential. It offers a powerful suite of applications like Photoshop, Illustrator, and After Effects, each designed to excel in specific design tasks.
Creative Cloud
Adobe Creative Cloud is my comprehensive toolkit for unleashing creative potential. It offers a powerful suite of applications like Photoshop, Illustrator, and After Effects, each designed to excel in specific design tasks.
Creative Cloud
Tap to flip
Adobe Creative Cloud is my comprehensive toolkit for unleashing creative potential. It offers a powerful suite of applications like Photoshop, Illustrator, and After Effects, each designed to excel in specific design tasks.
Creative Cloud
Tap to flip
WeChat is more than a messaging app—it’s my gateway to working with clients and collaborators in China. I use it to maintain seamless communication, build trusted relationships, and adapt to local business norms. It reflects my cultural adaptability and commitment to accessible, global consulting.
WeChat is more than a messaging app—it’s my gateway to working with clients and collaborators in China. I use it to maintain seamless communication, build trusted relationships, and adapt to local business norms. It reflects my cultural adaptability and commitment to accessible, global consulting.
Tap to flip
WeChat is more than a messaging app—it’s my gateway to working with clients and collaborators in China. I use it to maintain seamless communication, build trusted relationships, and adapt to local business norms. It reflects my cultural adaptability and commitment to accessible, global consulting.
Tap to flip
Services
01
Cybersecurity Risk Assessment
01
Cybersecurity Risk Assessment
01
Cybersecurity Risk Assessment
01
Cybersecurity Risk Assessment
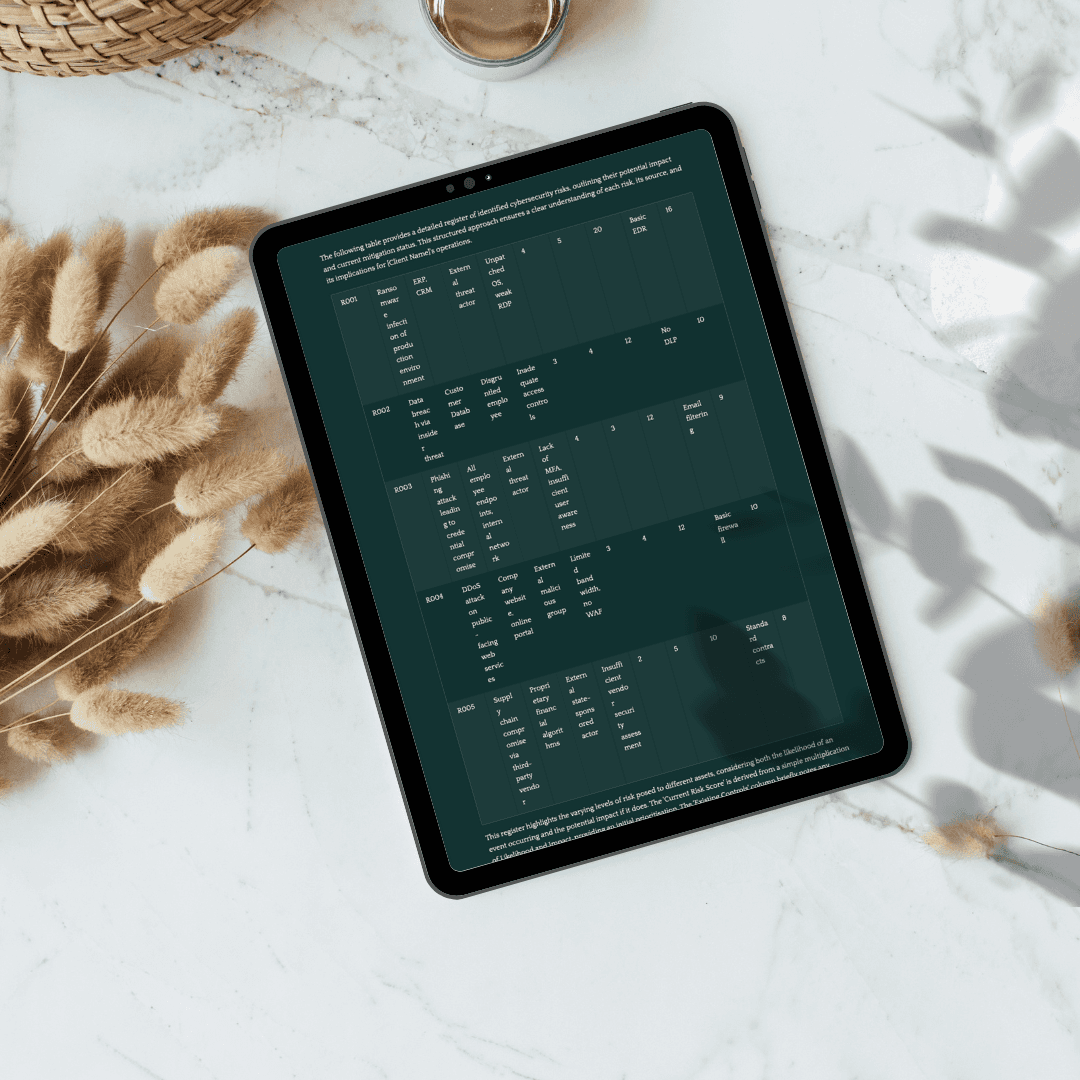
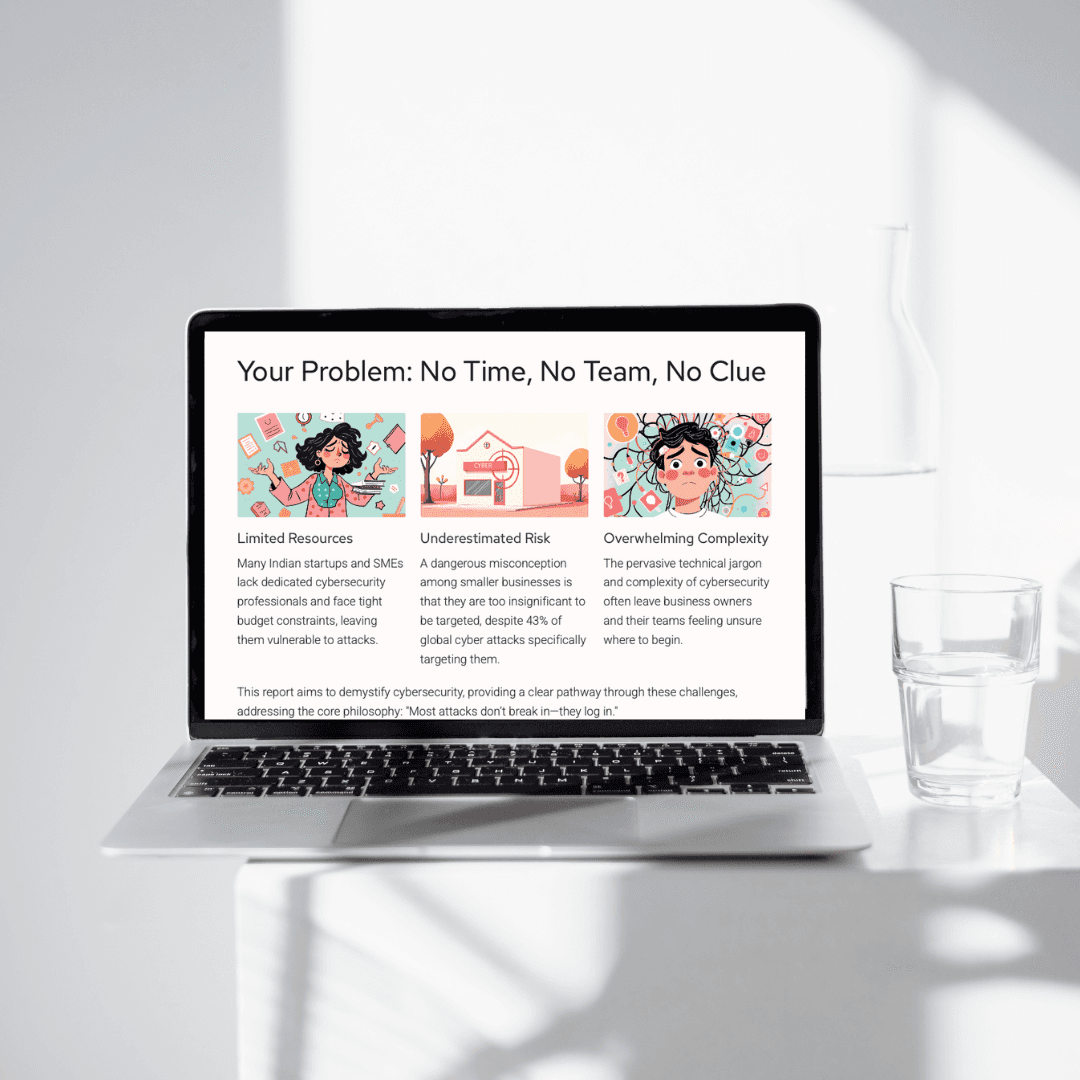
Transform your digital safety posture with a comprehensive risk assessment designed to identify vulnerabilities across your network, applications, and cloud services. Using industry-standard frameworks like NIST and ISO 27001, I evaluate threat exposure, business impact, and internal gaps to produce clear, actionable insights. Whether you’re a startup or an established enterprise, this service helps prioritise security investments and build resilience from the inside out.



Bridge the gap between compliance and clarity with advisory services tailored to regulations like GDPR, NIS2, ISO 27001, and SOC 2. I help you develop or refine security policies, data handling procedures, and access control frameworks—ensuring you’re not just compliant, but audit-ready. Whether you’re scaling fast or navigating your first certification, I simplify the process and embed sustainable governance into your operations.



02
Compliance & Policy Advisory
02
Compliance & Policy Advisory
Empower your people to become your first line of defence. This service includes realistic phishing simulations followed by custom training tailored to your team’s awareness gaps. You’ll receive reporting dashboards, engagement metrics, and a measurable increase in organisational cyber maturity—all without overwhelming your staff with jargon or fear.



03
Phishing Simulation & Awareness Training
03
Phishing Simulation & Awareness Training
Secure your move to the cloud with expert guidance across AWS, Azure, and GCP. I audit existing setups, strengthen IAM policies, and implement logging, WAFs, encryption, and security groups tailored to your environment. Whether you’re building a cloud-native app or migrating sensitive data, I make sure your stack is robust, scalable, and audit-friendly.



04
Cloud Security Consulting
04
Cloud Security Consulting
Be ready before the breach. I help organisations prepare for cybersecurity incidents with tailored response plans, escalation protocols, and runbook development. This service includes simulations and tabletop exercises that equip your team to act fast, reduce downtime, and minimise reputational damage when a real-world event occurs.



05
Incident Response Planning
05
Incident Response Planning
Secure your digital products with a comprehensive security audit. I evaluate your website or application against industry standards like OWASP Top 10, uncovering vulnerabilities such as misconfigurations, input flaws, or session weaknesses. Delivered with a remediation checklist, this audit helps you protect users and maintain trust.



06
Website & App Security Audit
06
Website & App Security Audit
Build a scalable governance model that aligns with your growth. I help startups and SMEs implement GRC (Governance, Risk, Compliance) frameworks using tools like OneTrust, Vanta, and Drata. Whether you’re preparing for ISO 27001, NIS2, or internal risk maturity, this service ensures operational accountability and strategic foresight.



07
GRC Implementation & Strategy
07
GRC Implementation & Strategy
Integrate security into every stage of your development lifecycle. I implement security testing into CI/CD pipelines, automate threat detection, and ensure code and infrastructure are aligned with compliance. Using tools like GitHub Actions, Zapier, and Bash scripts, I make security seamless—not a bottleneck.



08
Secure DevOps & Automation
08
Secure DevOps & Automation
Your brand is valuable—so is your digital identity. I offer continuous monitoring services to detect domain spoofing, impersonation attacks, leaked credentials, and fake profiles across the web. This service keeps your reputation clean, your users safe, and your digital footprint professionally managed.



09
Brand Protection & Digital Footprint Monitoring
09
Brand Protection & Digital Footprint Monitoring
Social platforms are often overlooked attack vectors. I audit your organisation’s social media presence for weak passwords, unmonitored accounts, risky third-party integrations, and exposure to impersonation. I also deliver platform-specific security checklists to help you stay safe while staying social.



10
Social Media Security Hygiene
10
Social Media Security Hygiene
Security doesn’t have to wait for scale. My Startup Security Kits provide early-stage ventures with practical essentials—policy templates, access control checklists, secure cloud configurations, and awareness training. It’s a plug-and-play foundation that earns user trust and supports investor confidence.



11
Startup Security Kits
11
Startup Security Kits
Working across borders? I help teams navigate regional compliance, secure collaboration, and cultural expectations, especially in regions like the EU and China. With support for tools like WeChat and region-specific risk assessments, this service ensures your cybersecurity practices are globally adaptive and locally informed.
12
Cross-Cultural Cyber Enablement
12
Cross-Cultural Cyber Enablement
Cybersecurity Support Plans for SMEs
Starter Support Plan
Perfect for local businesses, nonprofits, or early-stage startups taking their first cybersecurity steps.
Website & infrastructure risk scan
Basic cyber hygiene checklist
Stock photo integration
Guidance on password policies & backups
One free 30-minute consultation
Educational resources for your team
24/7 contact via email
Starter Support Plan
Perfect for local businesses, nonprofits, or early-stage startups taking their first cybersecurity steps.
Website & infrastructure risk scan
Basic cyber hygiene checklist
Stock photo integration
Guidance on password policies & backups
One free 30-minute consultation
Educational resources for your team
24/7 contact via email
Starter Support Plan
Perfect for local businesses, nonprofits, or early-stage startups taking their first cybersecurity steps.
Website & infrastructure risk scan
Basic cyber hygiene checklist
Stock photo integration
Guidance on password policies & backups
One free 30-minute consultation
Educational resources for your team
24/7 contact via email
Growth Enablement Plan
Ideal for organisations looking to strengthen their digital defence posture with practical, no-cost help.
Everything in Starter Plan
One-on-one security onboarding
Cloud or platform security review
Compliance alignment overview (NIS2, GDPR)
Basic incident response guidance
Monthly follow-up check-in
Community referrals and shoutouts
Growth Enablement Plan
Ideal for organisations looking to strengthen their digital defence posture with practical, no-cost help.
Everything in Starter Plan
One-on-one security onboarding
Cloud or platform security review
Compliance alignment overview (NIS2, GDPR)
Basic incident response guidance
Monthly follow-up check-in
Community referrals and shoutouts
Growth Enablement Plan
Ideal for organisations looking to strengthen their digital defence posture with practical, no-cost help.
Everything in Starter Plan
One-on-one security onboarding
Cloud or platform security review
Compliance alignment overview (NIS2, GDPR)
Basic incident response guidance
Monthly follow-up check-in
Community referrals and shoutouts
Need tailored support?
I design cybersecurity solutions to fit your organisation’s unique challenges. From risk assessments to resilience planning, let’s build a strategy that works for you. Contact me for a consultation and custom plan.